KubeOps PLATFORM
Optimum security and flexibility for the modern management of your Kubernetes clusters.
Maximum security and compliance for KRITIS applications
KubeOps PLATFORM is the solution for demanding applications in critical infrastructure areas (KRITIS) and places the highest value on security and data protection standards. Specially designed for the efficient provision, management and scaling of Kubernetes clusters, it strictly complies with GDPR regulations as well as ISO 27001 and ITIL requirements. With this strong focus on security and compliance, KubeOps positions itself as the preferred choice for use in sensitive and critical environments.
KubeOps PLATFORM is committed to providing the best Kubernetes solution on the market with continuous updates, improvements and support.
Digital sovereignty redefined -
The KubeOps PLATFORM
Stay confident and flexible with the KubeOps PLATFORM. Maximum control over your IT infrastructure without compromise
The KubeOps PLATFORM ensures that applications are operated unchanged. The PLATFORM is highly available and scalable. Regardless of whether you operate your infrastructure on-premises, in the cloud or in hybrid scenarios - your applications are operated securely and in compliance with the law.
Our sovereign solution avoids dependencies on proprietary technologies and providers. PLATFORM is based on open standards and offers you the flexibility to relocate workloads as required.
Workloads can be moved seamlessly between different environments to dynamically adapt to business requirements. This not only increases efficiency, but also reduces potential risks.
By complying with standards such as GDPR (DSGVO), ISO 27001 and NIS2, you remain legally protected. PLATFORM ensures that your IT infrastructure meets the highest data protection and security requirements.
Benefit from a robust security architecture that actively detects and fends off threats and makes your IT infrastructure future-proof.

Simplifying Secure K8s Clusters
deployment, management and scaling
KubeOps Platform involves all the activities required to run, manage and maintain Kubernetes clusters in production environments, including our best practices, self-deployed tools and strategies.
high level security
KubeOps Platform sets up your clusters with a strong focus on security. These clusters can be audited by the German Federal Office for Information Security (BSI).
Our managed service solutions
We also take care of the operational aspects of your cluster and offer managed service solutions if required.
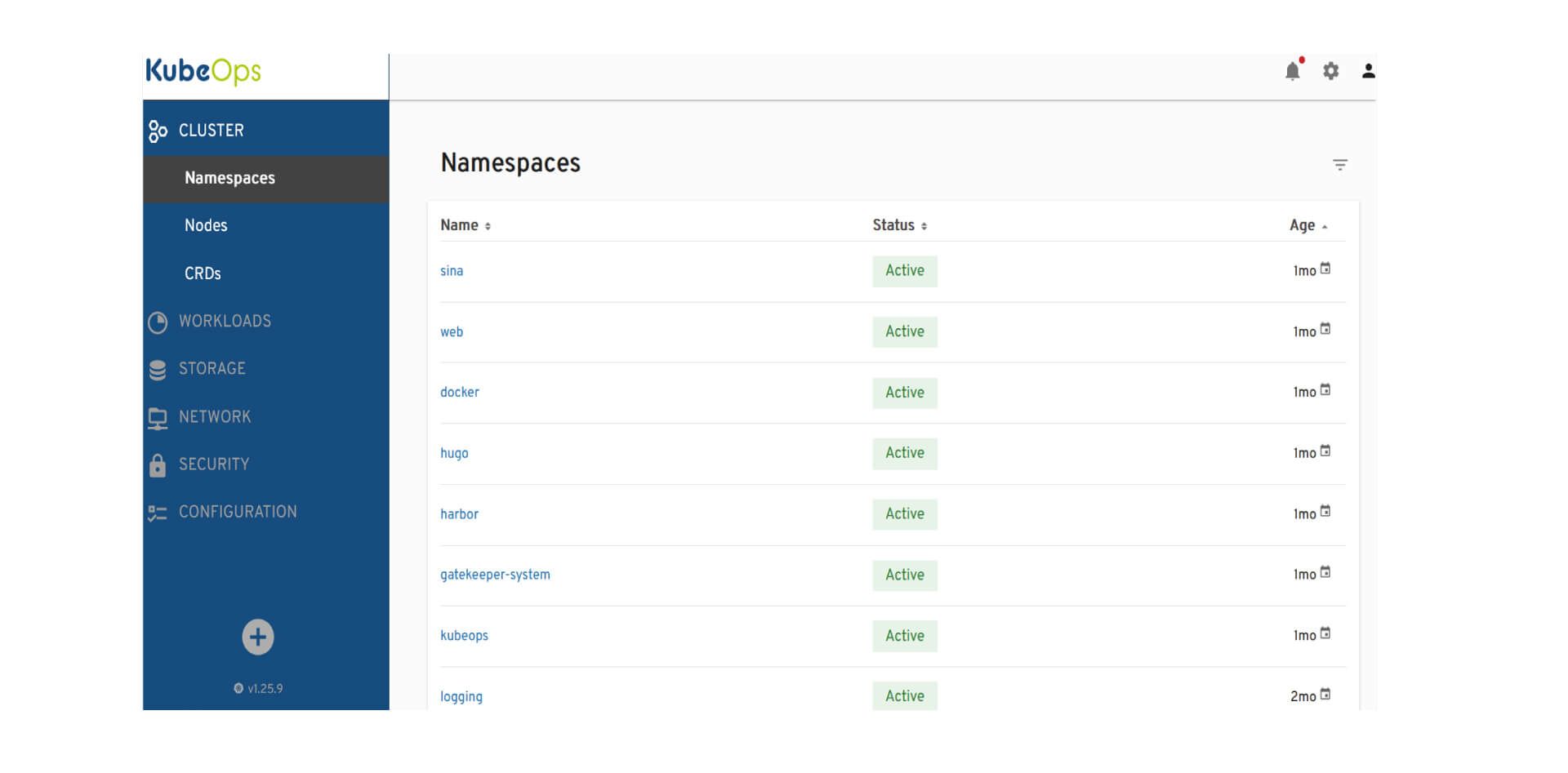
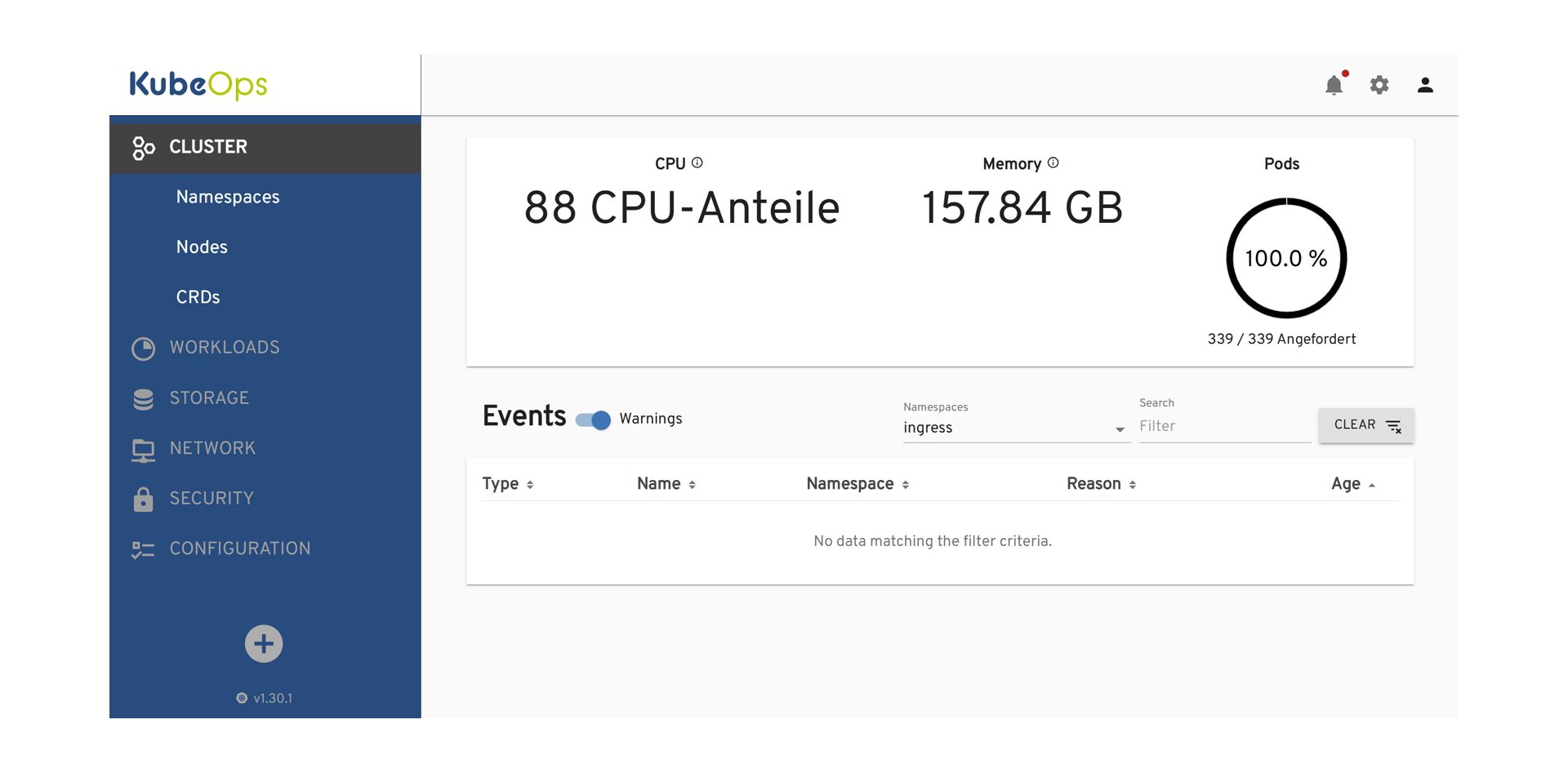
User können im KubeOps Dashboard Namespaces überblicken und verwalten.
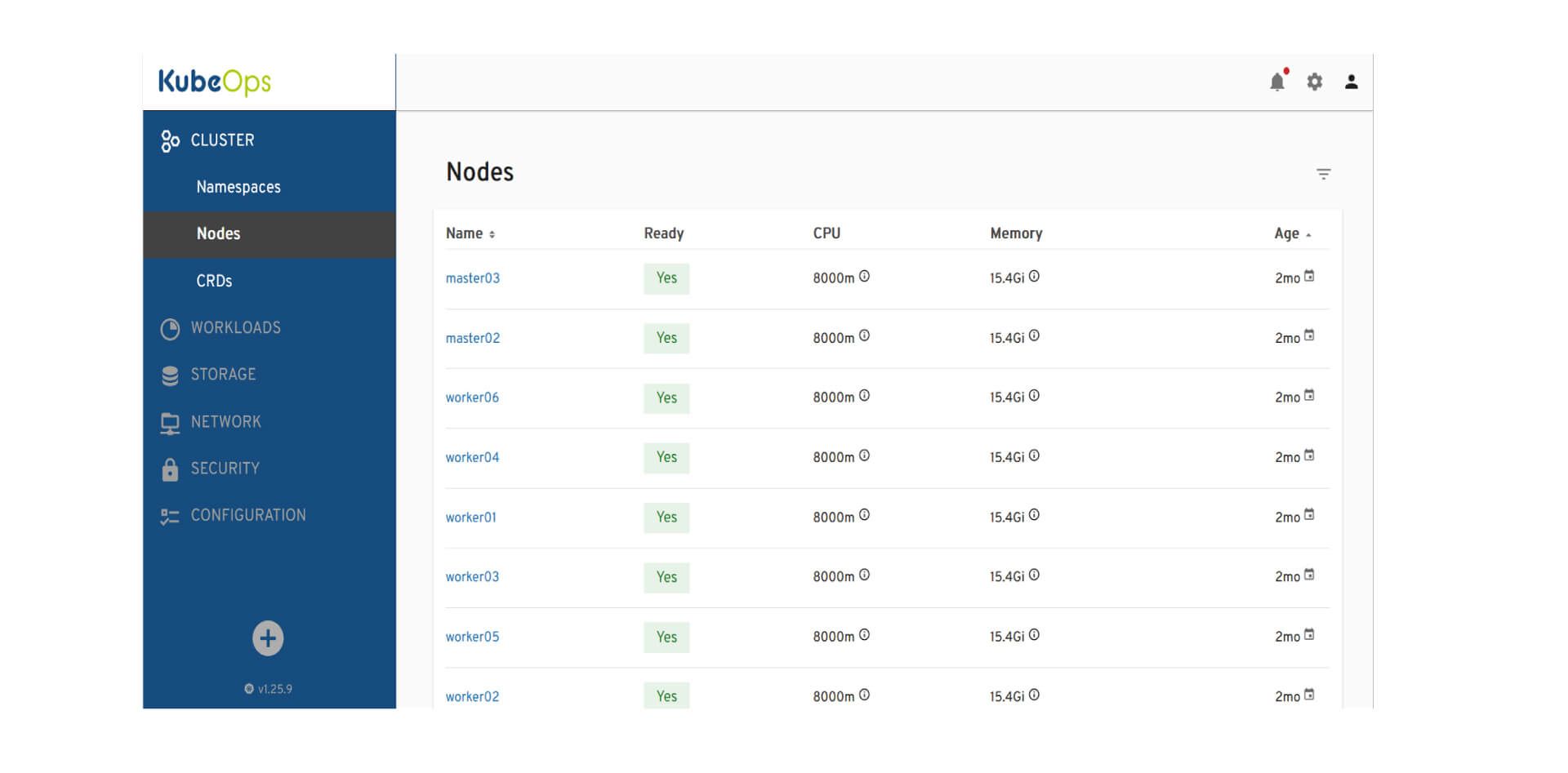
User können den Zustand und die Leistung der Cluster-Knoten überwachen und verwalten.
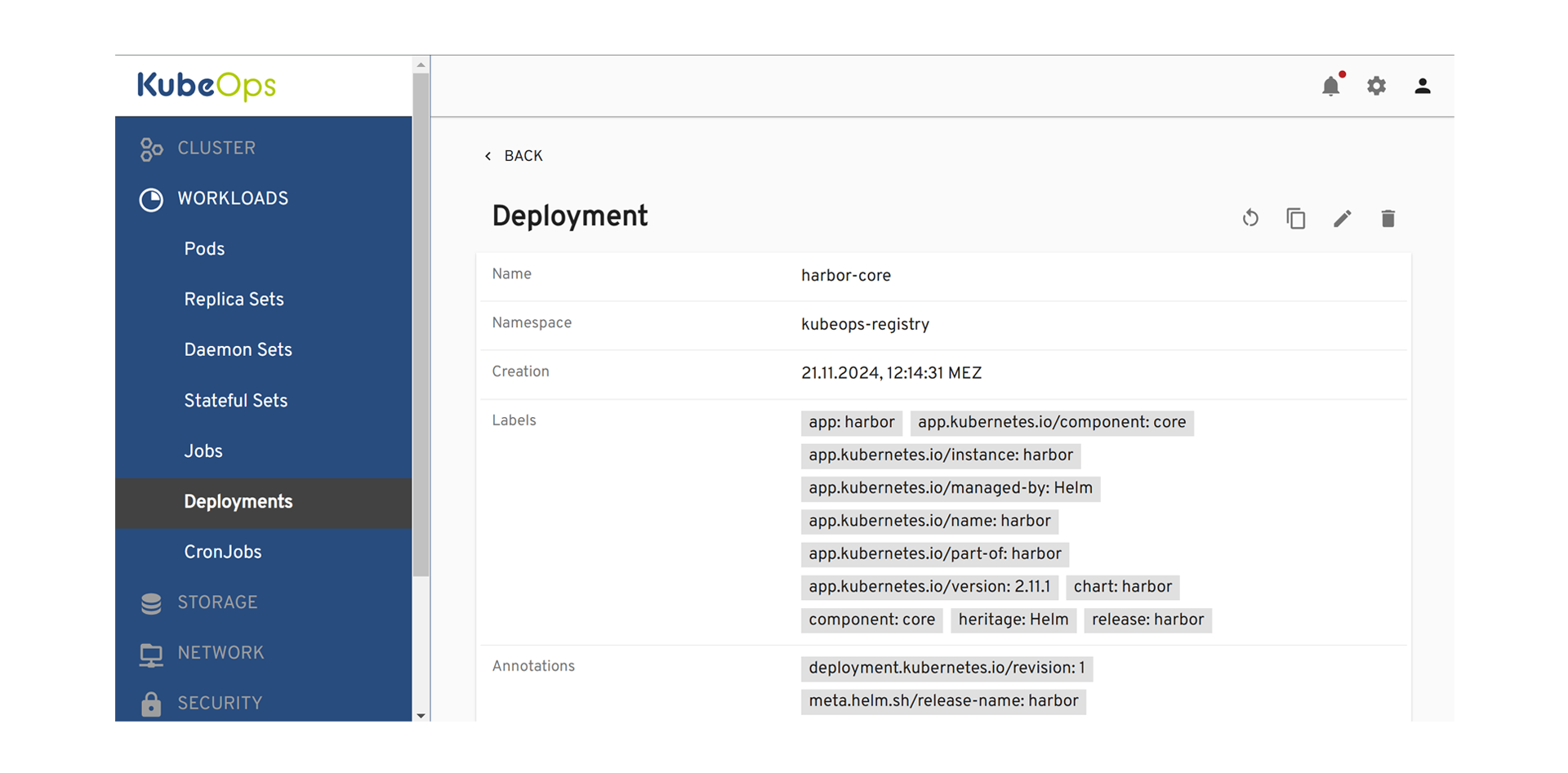
Detailansicht eines Prometheus-Grafana Deployments im KubeOps Dashboard.
Bearbeitung der Deployment-Konfiguration im KubeOps Dashboard.
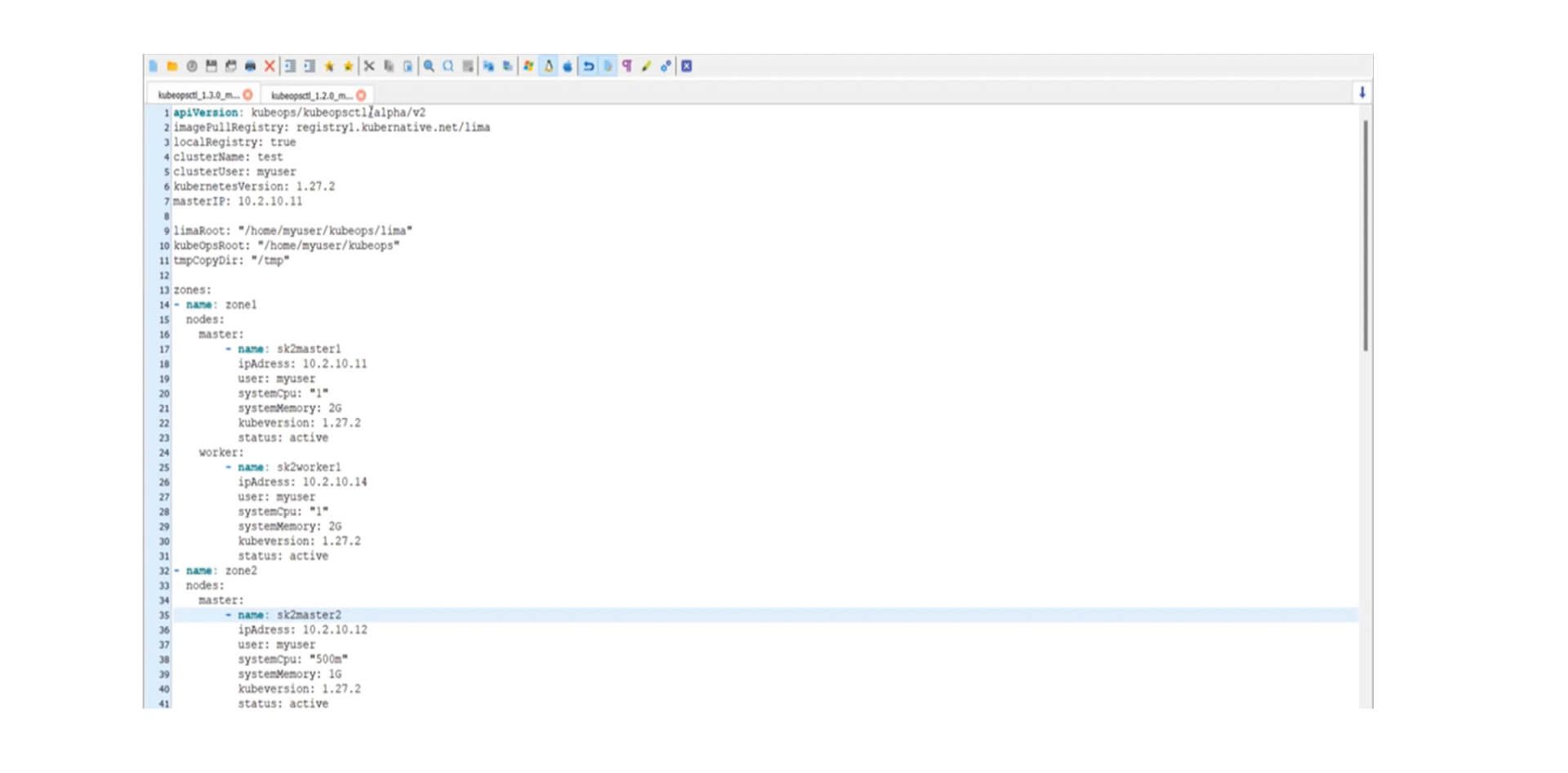
Kubeopsctl ermöglicht die effiziente Verwaltung und Automatisierung von Clustern.
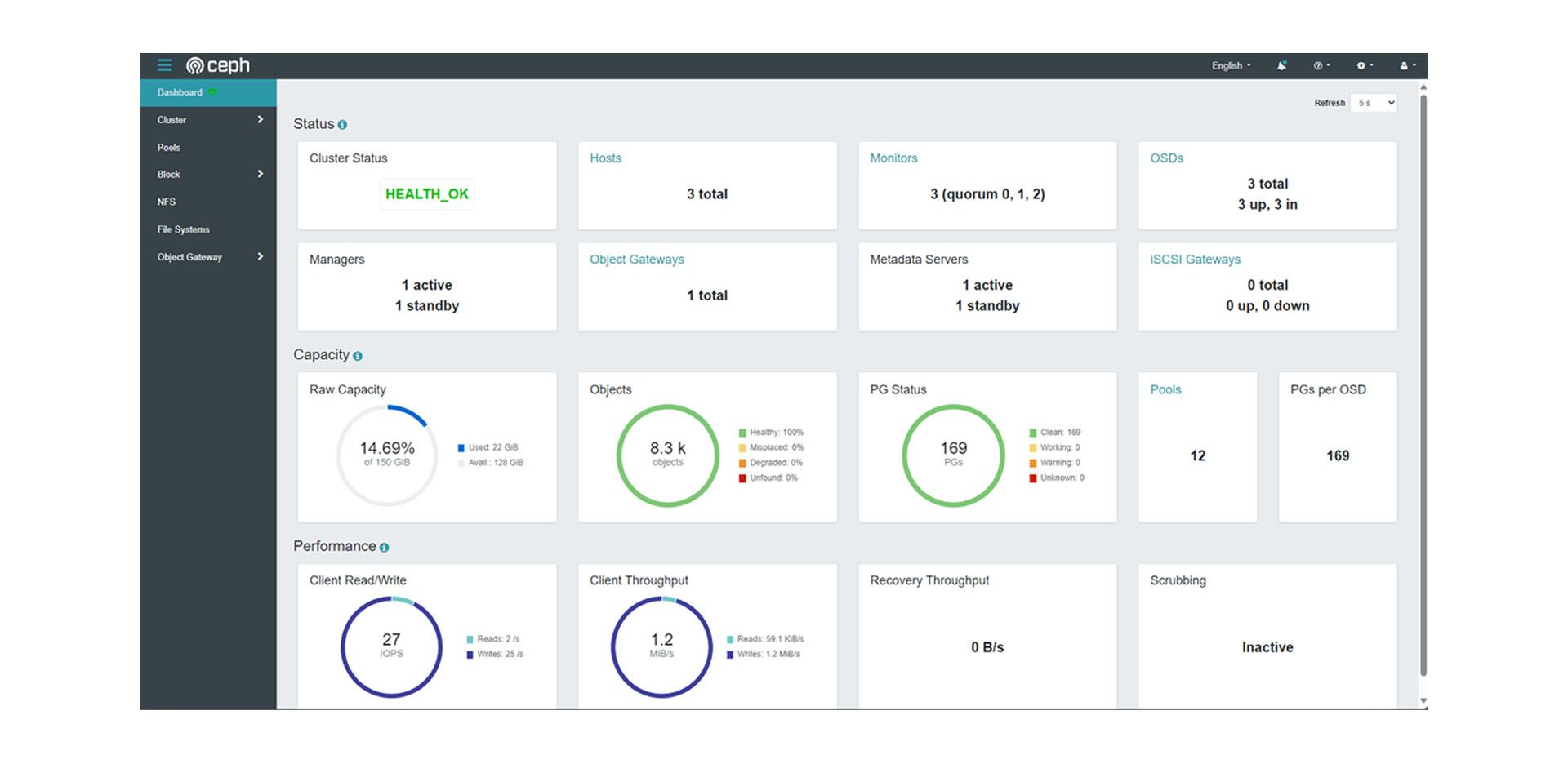
Durch das ceph Dashboard können die Vorgänge und die Auslastung beobachtet werden.
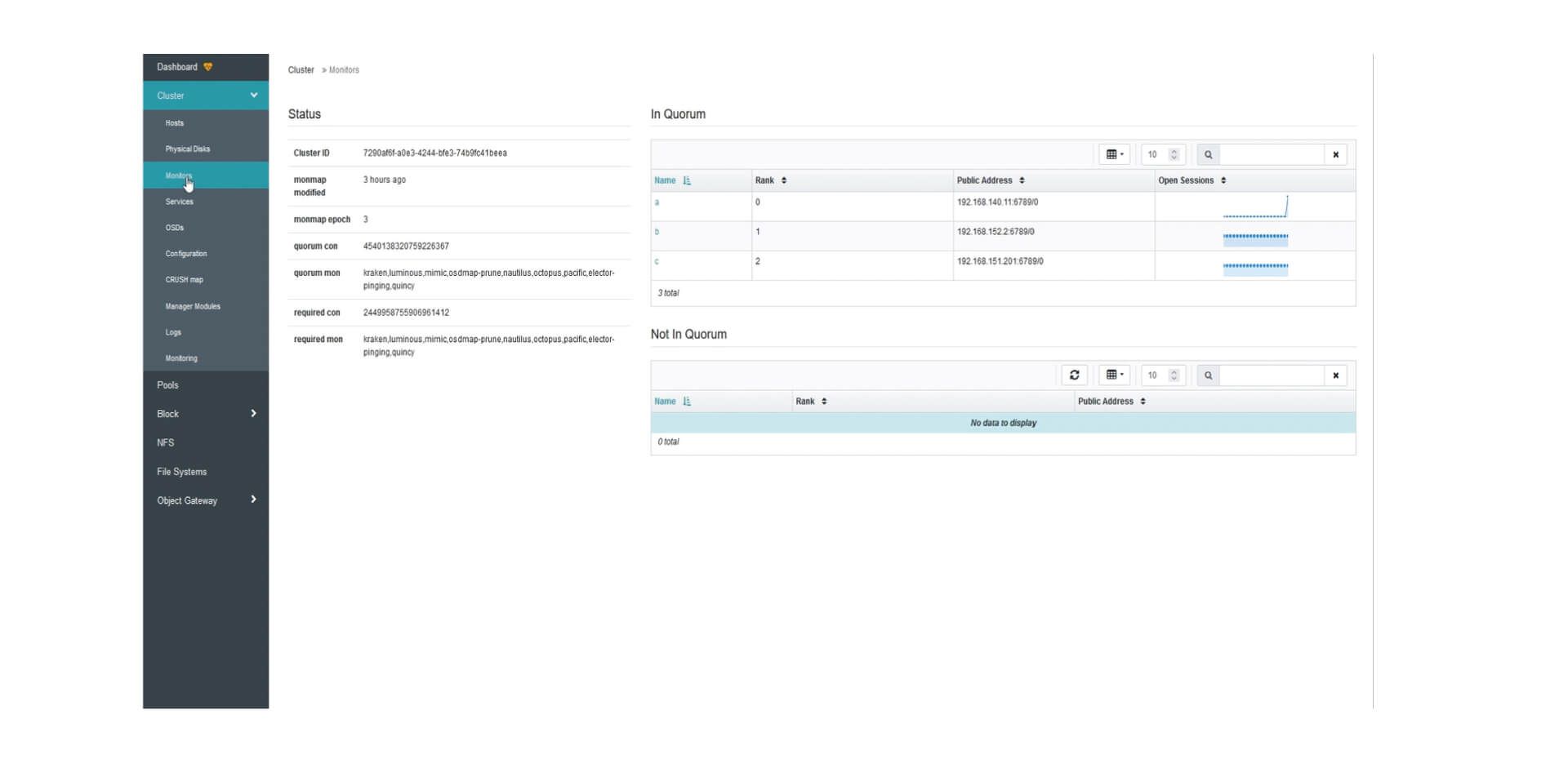
Ceph Monitors ermöglicht die Überwachung der Verfügbarkeit und Gesundheit der Cluster.
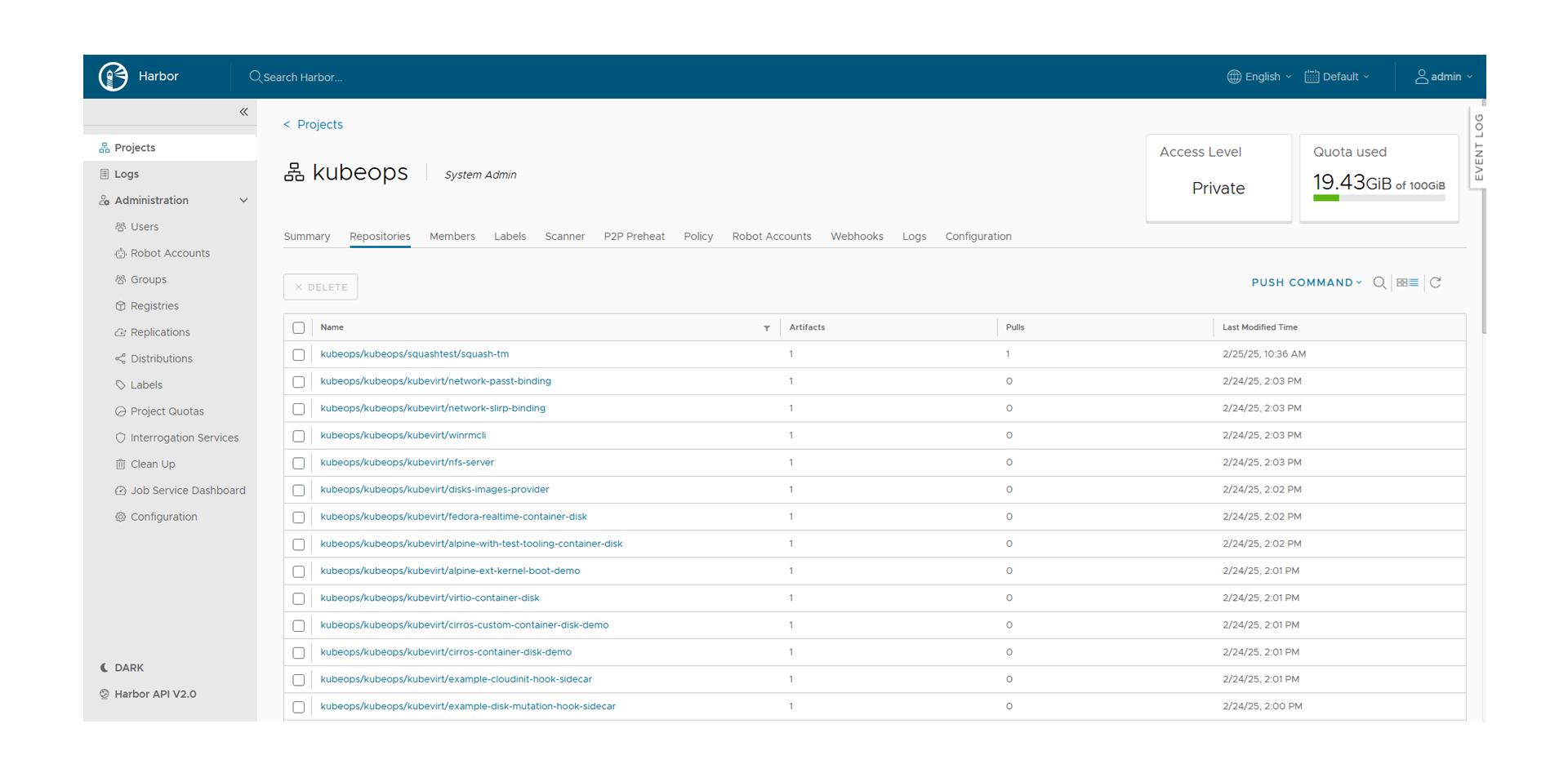
Harbor Logs zum Debuggen, Überwachen und Sicherstellen der Compliance.
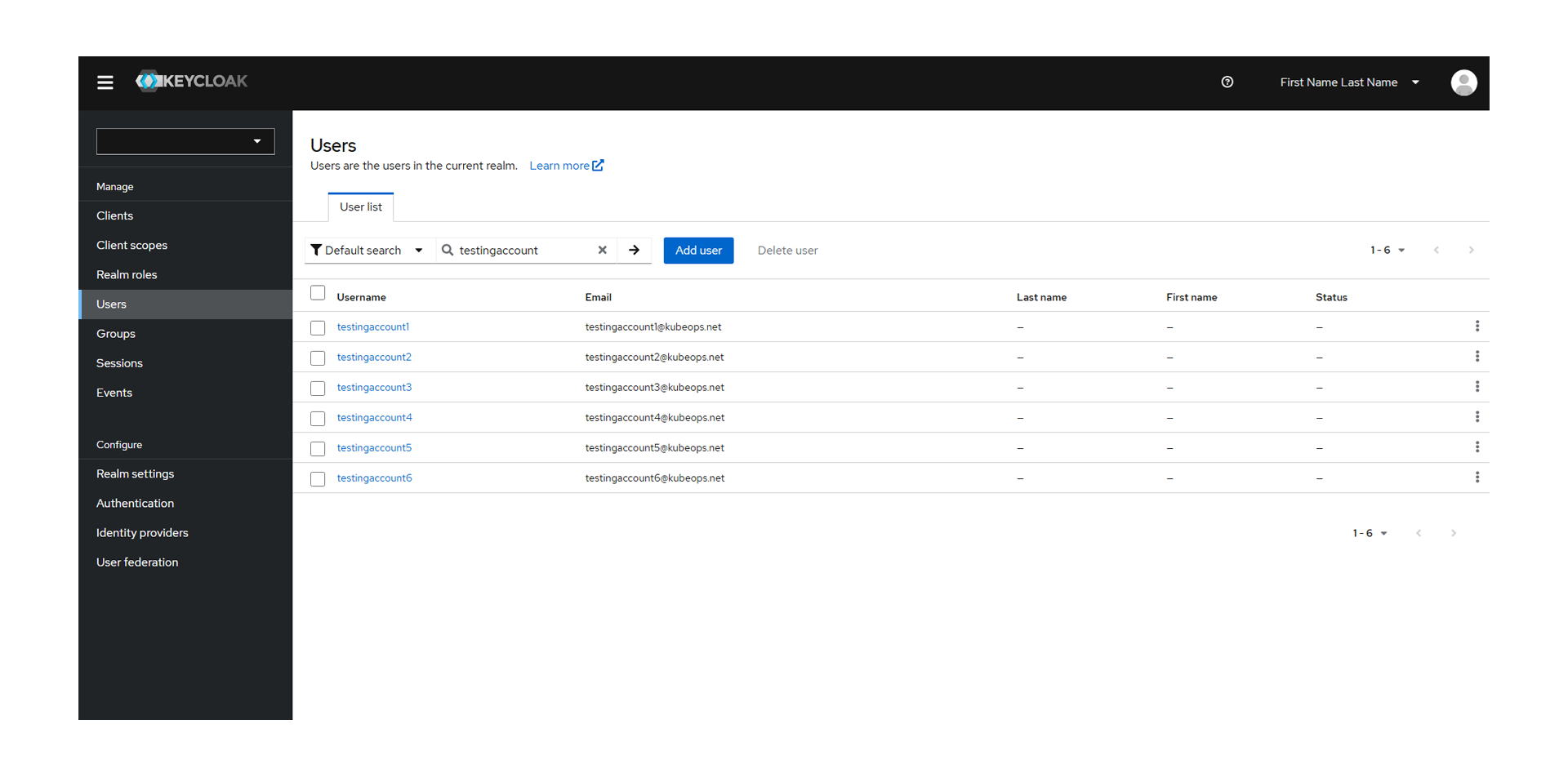
Keycloak als Identity-Management-System und zentraler Zugriff auf Dashboards.
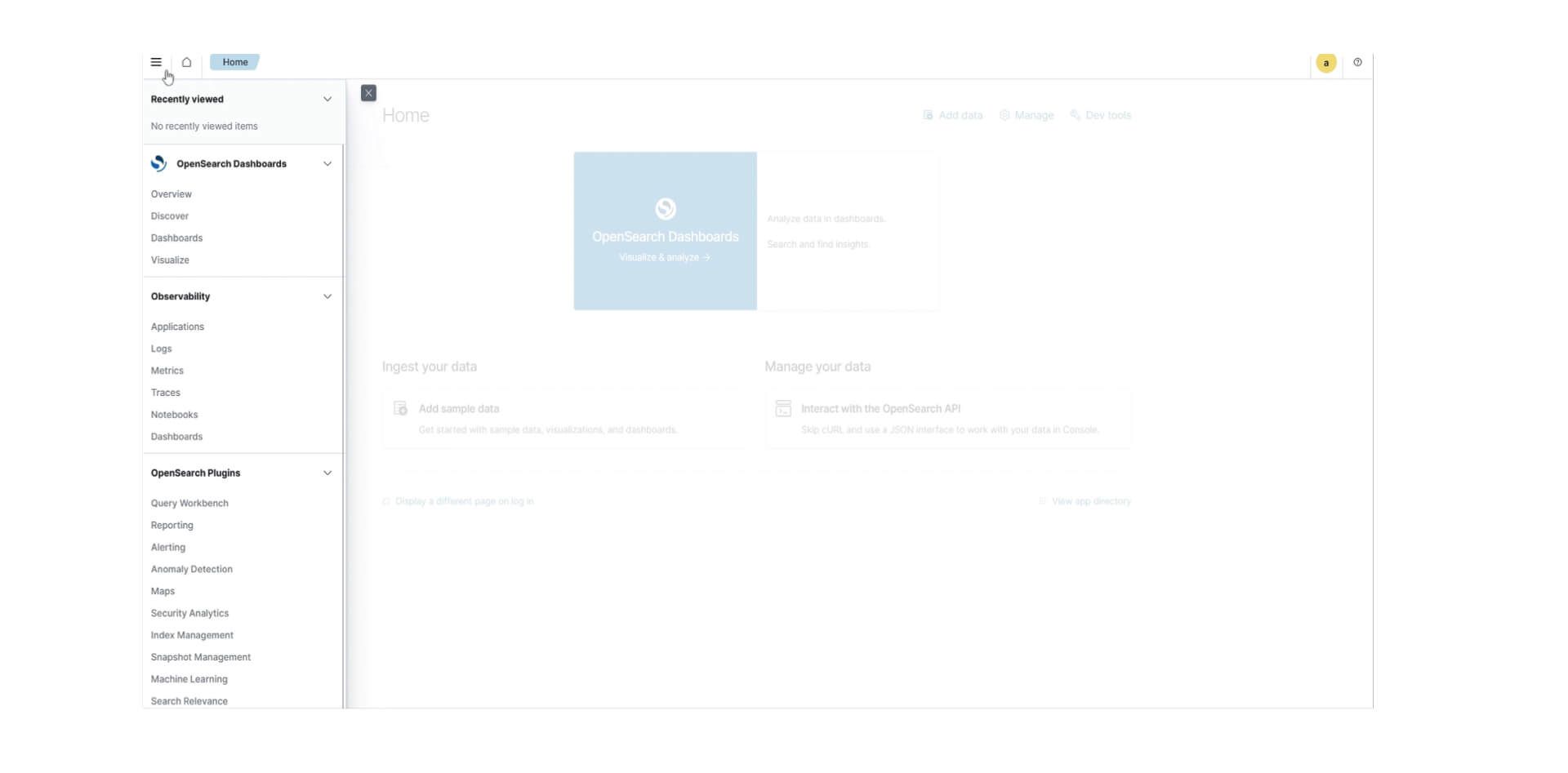
Das OpenSearch Dashboard ermöglicht es Usern, Daten zu visualisieren und zu analysieren.
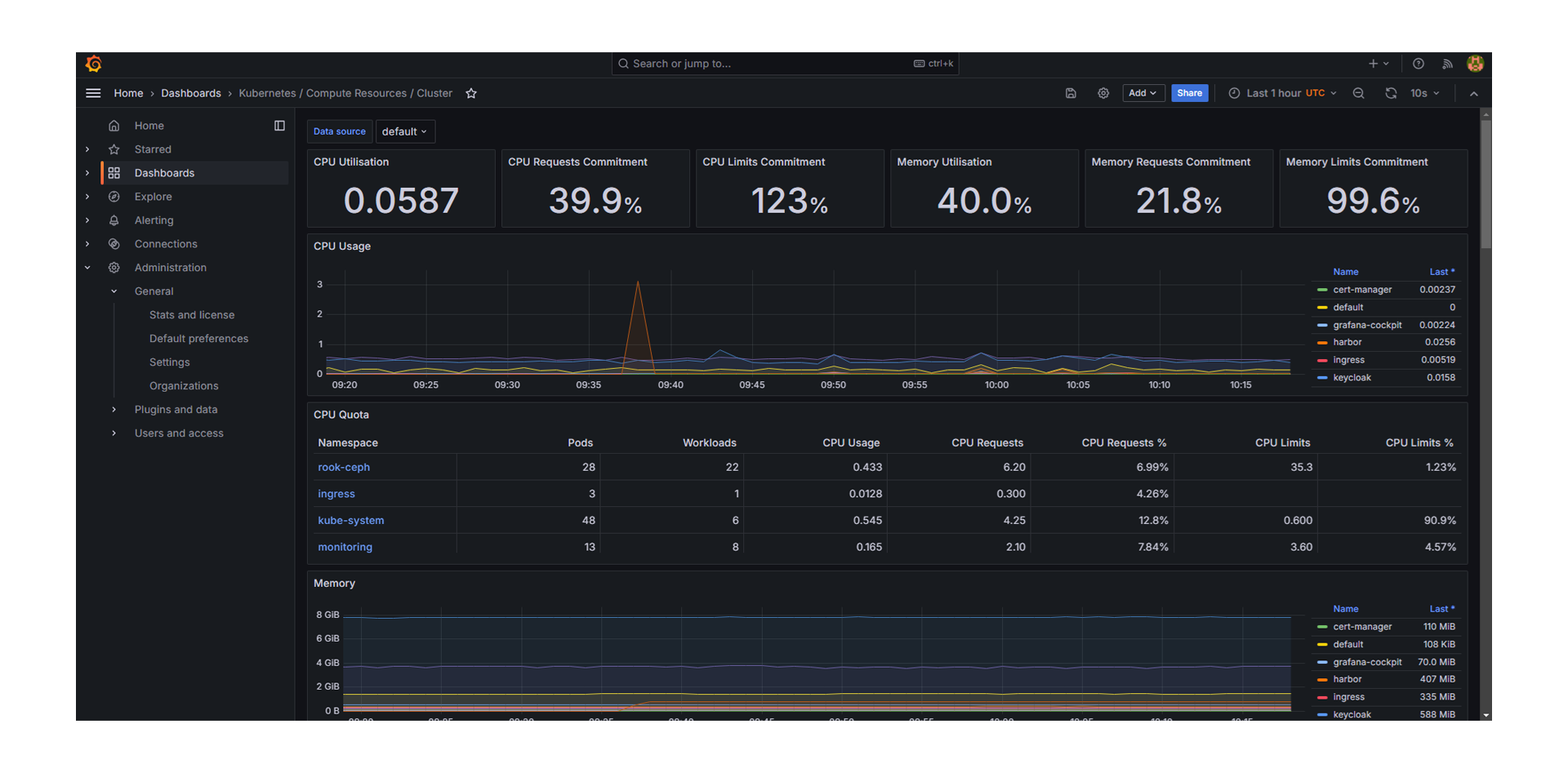
Anzeigen von Downtimes und Einrichtung von Alarmings mit Grafana.
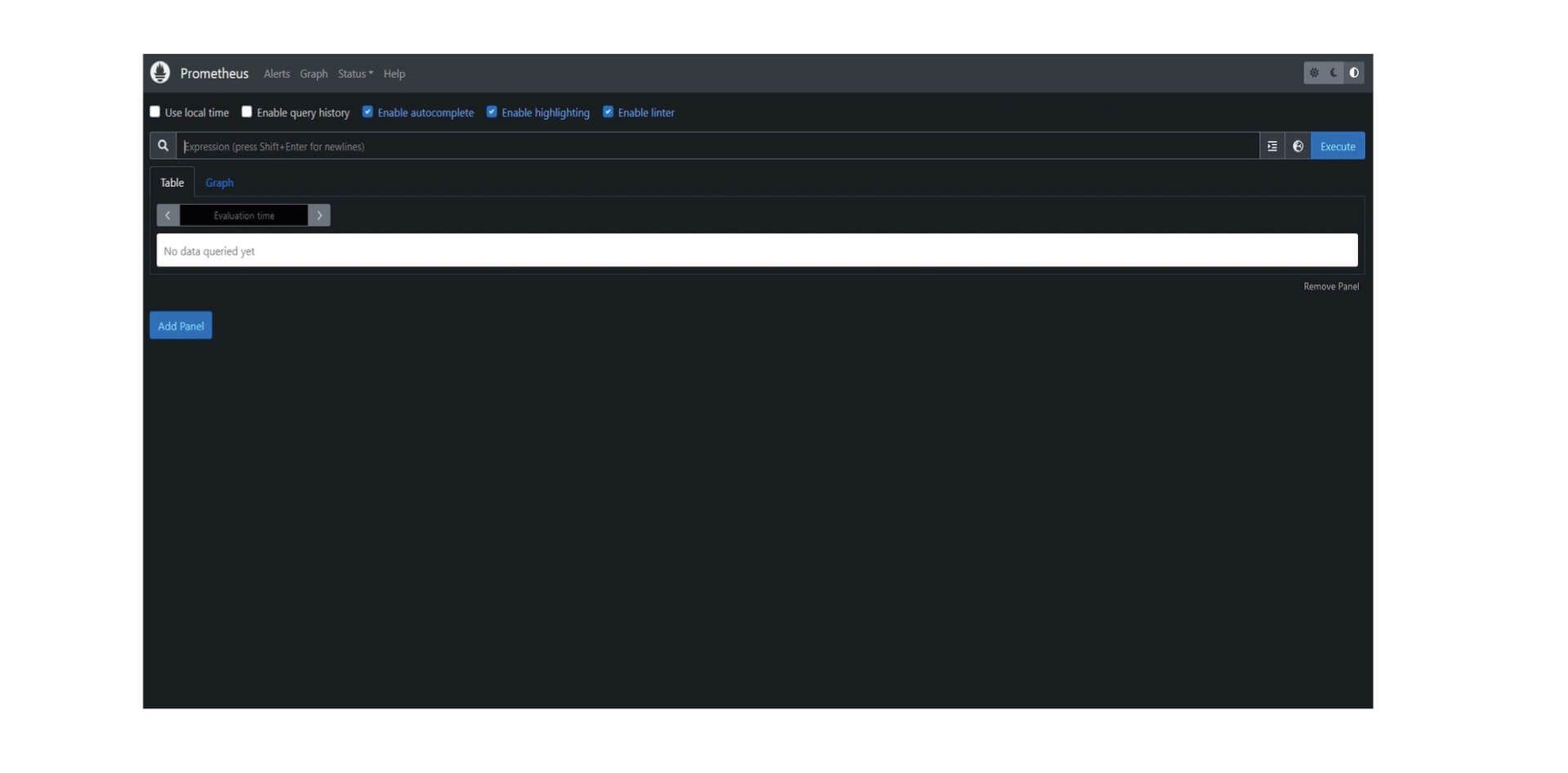
Monitoring und Alarmierung von Kubernetes-Clustern durch Prometheus.

KubeOps PLATFORM runs everywhere
KubeOps PLATFORM only requires a clean OS installation for its nodes to create and operate clusters through there complete life-cycle. KubeOps PLATFORM brings production ready K8s to all hypervisors and bare metal!
public cloud
IT infrastructure and services are accessible via internet.
private cloud
An exclusive cloud infrastructure available only to one organization, featuring enhanced security and control over data.
on-premise
Kubernetes clusters are deployed on company-owned servers, e.g. in their own data centers.
Features and tools of the PLATFORM
The included features and tools are designed to simplify the deployment, management and scaling of Kubernetes clusters with a focus on high level security.
- All Features
- All Tools
- Cluster Management
- Kubernetes with Disaster Recovery
- Network
- Observability
- Security
- Storage
automatic setup
Repeatable and easy setup allows you to manage your clusters with infrastructure as code. Build your KubeOps PLATFORM cluster from the OS layer with everything you need and configured however you like.
backup and restore
A complete backup solution is a must have for operating a stateful infrastructure. Enables all the Kubernetes objects you rely on to be securely stored in an object store of your choice.

Calico

cert manager

containerd

fileBeat

Firewall

Grafana

Harbor

Helm

high availability
Ensuring continuous operations is one of our highest goals. Kubernetes is an amazing starting point for high availability, but still leaves some single points of failure. We address these issues, like remote image registries and standalone load balancers, with custom peer-to-peer systems, and integrated failure zones, to enable zero downtime maintenance. This allows for all your infrastructure to be as reliable as possible.

integrated storage
Most real-world applications require persistent storage that is fast and reliable. Integrated storage allows us to provide a fantastic cloud native storage solution out of the box. Production ready management for file, block and object storage with the flick of a switch.

K8s

Kubeadm

KubeOps KOSI

logging and monitoring
KubeOps PLATFORM gives you the capability to centralize all relevant information about your infrastructure and application. Monitoring them continuously and alerting you, however you choose.

Logstash
multi networking
The capability to deploy multiple networks side by side in the same cluster allows for increased security measures and simple zero downtime migration to other network plugins.

Multus

NFTables

nginx

Open Policy Agent

OpenSearch

Podman

policy enforcement
Your infrastructure, your rules. Limit, modify and enhance all changes to your cloud with state-of-the-art policy enforcement.

Prometheus

Red hat

Rook

secured supply chain
Sourcing Software for your infrastructure is a critical attack surface. KubeOps PLATFORM binds your application into repeatable transferable artefacts. Stage from your laptop till production without worrying about the images you need to power your applications. Wherever you move they follow.

security
All products we provide undergo a multistage security examination. And are continuously monitored for the latest vulnerabilities. Most publicly available packages contain critical vulnerabilities that endanger your systems of not removed before integrating them. The platform has the capability to be installed in a highly secured isolated environment (Air Gap).

Trivy














